-
Notifications
You must be signed in to change notification settings - Fork 163
System Information
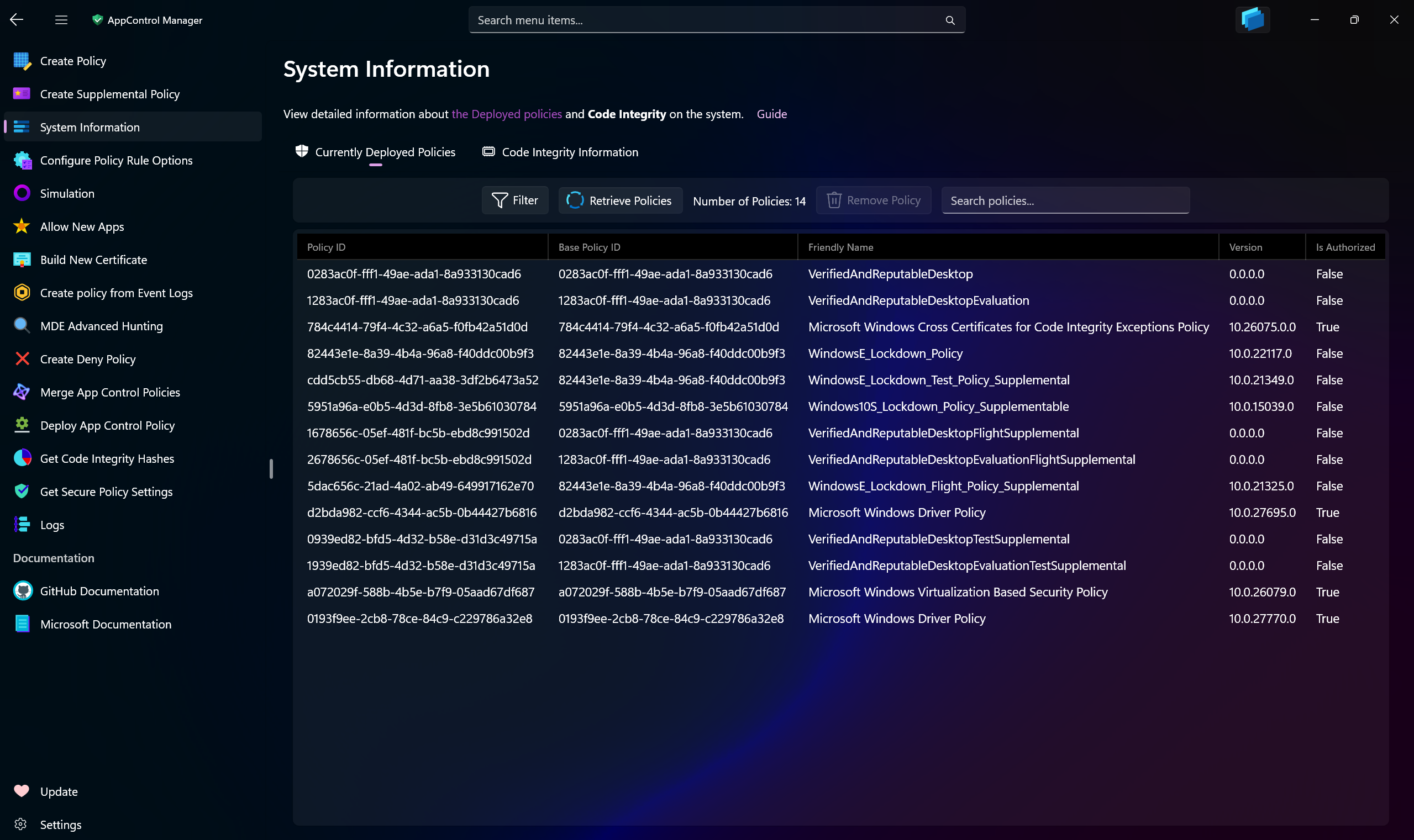
Use the System Information page in AppControl Manager to view details about the deployed App Control policies on the system.
-
Search through the list of policies
-
View the rule options in each policy
-
Determine which policy is signed or unsigned (requires Windows 11 24H2 or later/Windows Server 2025 or later, otherwise all policies will appear as
unsignedregardless of their actual signing status) -
Sort the policies using multiple criteria
-
See which policy is Base, Supplemental or System
-
View the version of each policy
Tip
You can view the version of the Microsoft Vulnerable Driver Block List in this page by checking the box for including System policies in the list.
In the Code Integrity Information section you can view advanced details about the current status of Code Integrity on the system.
You can also check the status of Application Control for Business, including whether User-Mode or Kernel-Mode policies are deployed and whether they are set to Enforced mode or Audit mode.
This page also allows you to remove the deployed non-system App Control policies from the system.
Whenever you select a policy from the list, the app will automatically present to you the best and most appropriate course of action in order to remove it.
Unsigned Base or signed/unsigned Supplemental Application Control policies can be removed with a single click/tap of a button. Simply select a policy from the list and then use the Remove button to remove it.
Starting with Windows 11 24H2/Windows Server 2025, no reboot is required for unsigned base or supplemental policies.
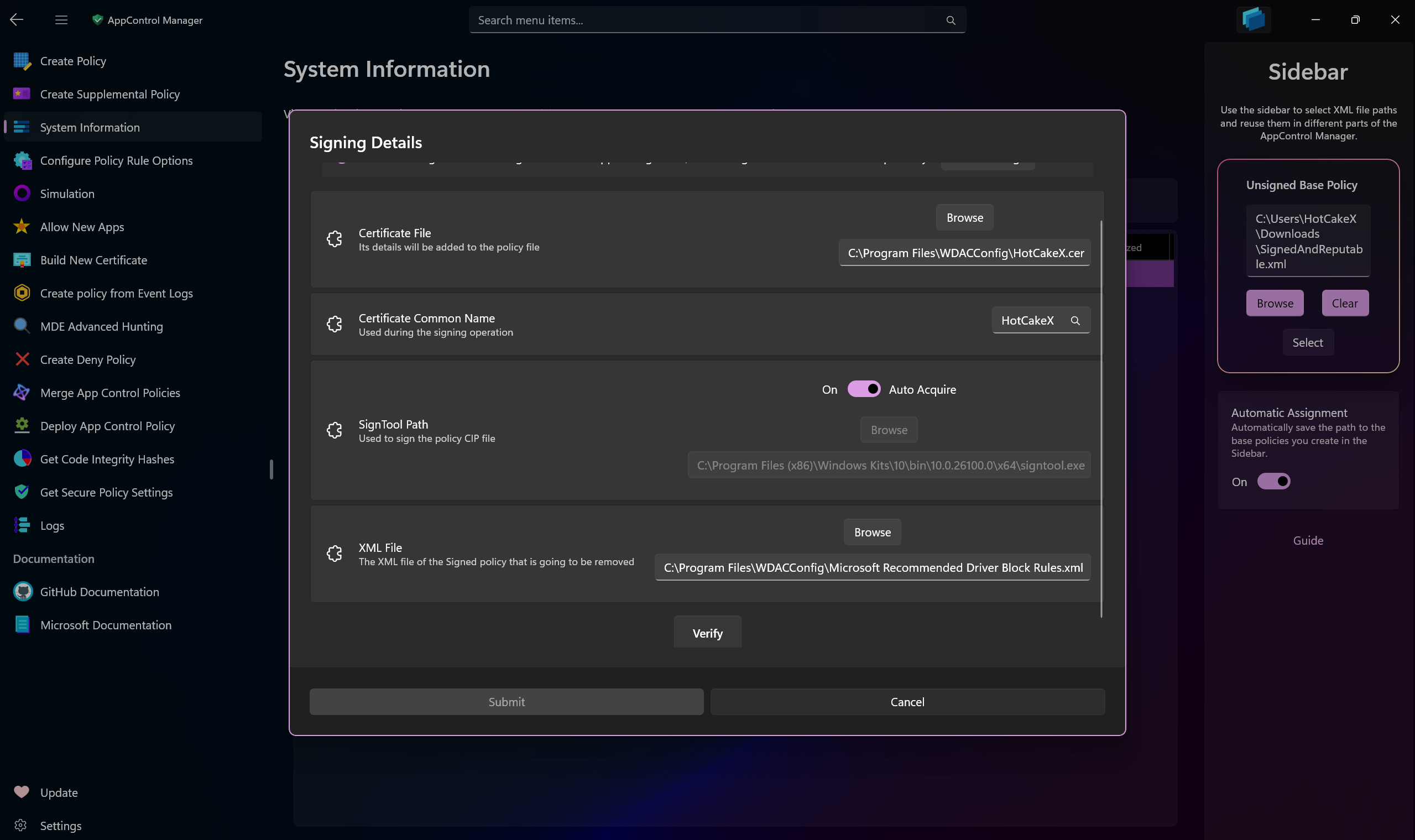
Signed Base policies require additional information during the removal process. Select a signed policy and then press the Remove button, you will be presented with a dialog asking for additional information.
-
Certificate File: Provide the path to the certificate
.cerfile. The certificate's details must exist in the XML policy file as signers, so ensure it is the same certificate that you used to sign the policy with. The certificate must exist in the Personal store of the Current User certificate stores with private key. -
Certificate Common Name: The Common Name (CN) of the same certificate file you select.
-
SignTool Path: The path to the
SignTool.exe. If you don't have it, you can toggle the Auto Acquire switch. Auto Acquire will try to first find it on the system by checking for installed Windows SDK, if it cannot find it, it will download it from the official Microsoft server. -
XML File: The path to the XML policy file of the same policy you're trying to remove from the system.
Once all four fields are populated, press the Verify button. This action validates your inputs and enables the Submit button, allowing you to proceed with the removal process. All of the information you submit will be saved in app settings so that the next time they will be automatically populated for you.
Following this step, the policy will be re-signed and redeployed on the system with a new rule option labeled Enabled: Unsigned System Integrity Policy.
Important
After completing this process, restart your system. Since signed policies are tamper-resistant, they leverage Secure Boot and reside in the EFI partition. Upon reboot, select the same signed policy and press the Remove button. The AppControl Manager will detect the policy as safe for removal and delete it from the system without requiring further input. (If you do not reboot your system and attempt to remove the signed policy that was just re-signed and re-deployed, it will lead to boot failure.)
Note
About the Automatic Policies filter option
Enabling this checkbox includes supplemental policies named AppControlManagerSupplementalPolicy in the displayed results. Each base policy created and deployed via the AppControl Manager automatically deploys a corresponding supplemental policy with this name. This supplemental policy is essential for the operation of the AppControl Manager application itself.
In addition, it contains a FilePublisher rule for SignTool.exe, allowing signing operations to be performed. If you intentionally remove this policy, you will no longer be able to launch the AppControl Manager or use SignTool.exe when certain base policies are active.
Note that these supplemental policies are automatically removed when their associated base policy is removed from the system, so no additional action is required on your part.
You can view the XML source of the AppControlManagerSupplementalPolicy supplemental policy here.
- Create AppControl Policy
- Create Supplemental Policy
- System Information
- Configure Policy Rule Options
- Simulation
- Allow New Apps
- Build New Certificate
- Create Policy From Event Logs
- Create Policy From MDE Advanced Hunting
- Create Deny Policy
- Merge App Control Policies
- Deploy App Control Policy
- Get Code Integrity Hashes
- Get Secure Policy Settings
- Update
- Sidebar
- Introduction
- App Control for Lightly Managed Devices
- App Control for Fully managed device - Variant 1
- App Control for Fully managed device - Variant 2
- App Control for Fully managed device - Variant 3
- App Control for Fully managed device - Variant 4
- App Control Notes
- How to Create and Deploy a Signed App Control Policy
- Fast and Automatic Microsoft Recommended Driver Block Rules updates
- App Control policy for BYOVD Kernel mode only protection
- EKUs in App Control for Business Policies
- App Control Rule Levels Comparison and Guide
- Script Enforcement and PowerShell Constrained Language Mode in App Control Policies
- How to Use Microsoft Defender for Endpoint Advanced Hunting With App Control
- App Control Frequently Asked Questions (FAQs)
- Create Bootable USB flash drive with no 3rd party tools
- Event Viewer
- Group Policy
- How to compact your OS and free up extra space
- Hyper V
- Overrides for Microsoft Security Baseline
- Git GitHub Desktop and Mandatory ASLR
- Signed and Verified commits with GitHub desktop
- About TLS, DNS, Encryption and OPSEC concepts
- Things to do when clean installing Windows
- Comparison of security benchmarks
- BitLocker, TPM and Pluton | What Are They and How Do They Work
- How to Detect Changes in User and Local Machine Certificate Stores in Real Time Using PowerShell
- Cloning Personal and Enterprise Repositories Using GitHub Desktop
- Only a Small Portion of The Windows OS Security Apparatus
- Rethinking Trust: Advanced Security Measures for High‐Stakes Systems
- Clean Source principle, Azure and Privileged Access Workstations
- How to Securely Connect to Azure VMs and Use RDP
- Basic PowerShell tricks and notes
- Basic PowerShell tricks and notes Part 2
- Basic PowerShell tricks and notes Part 3
- Basic PowerShell tricks and notes Part 4
- Basic PowerShell tricks and notes Part 5
- How To Access All Stream Outputs From Thread Jobs In PowerShell In Real Time
- PowerShell Best Practices To Follow When Coding
- How To Asynchronously Access All Stream Outputs From Background Jobs In PowerShell
- Powershell Dynamic Parameters and How to Add Them to the Get‐Help Syntax
- RunSpaces In PowerShell
- How To Use Reflection And Prevent Using Internal & Private C# Methods in PowerShell
