-
Notifications
You must be signed in to change notification settings - Fork 163
New DenyWDACConfig
New-DenyWDACConfig
[-Normal]
-PolicyName <String>
[-ScanLocations <DirectoryInfo[]>]
[-Deploy]
[-Level <String>]
[-Fallbacks <String[]>]
[-SpecificFileNameLevel <String>]
[-NoUserPEs]
[-NoScript]
[-Confirm]
[<CommonParameters>]Creates a Deny base policy by scanning a directory. The base policy will have 2 allow all rules, meaning it can be deployed as a standalone base policy, side-by-side any other Base/Supplemental policies.
Add a descriptive name for the Deny base policy. Accepts only alphanumeric and space characters.
| Type: | String |
|---|---|
| Position: | Named |
| Default value: | None |
| Required: | True |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Accepts one or more comma separated folder paths. Supports argument completion, when you press tab, folder picker GUI will open allowing you to easily select a folder, you can then add a comma , and press tab again to select another folder path or paste a folder path manually, works both ways.
| Type: | DirectoryInfo[] |
|---|---|
| Position: | Named |
| Default value: | None |
| Required: | True |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Indicates that the module will automatically deploy the Deny base policy after creation.
| Type: | SwitchParameter |
|---|---|
| Position: | Named |
| Default value: | None |
| Required: | False |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Offers the same official Levels to scan the specified directory path(s).
| Type: | String |
|---|---|
| Position: | Named |
| Default value: | WHQLFilePublisher |
| Required: | False |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Offers the same official Fallbacks to scan the specified directory path(s).
| Type: | String[] |
|---|---|
| Position: | Named |
| Default value: |
FilePublisher,Hash
|
| Required: | False |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
More info available on Microsoft Learn
| Type: | String |
|---|---|
| Position: | Named |
| Accepted values: |
OriginalFileName, InternalName, FileDescription, ProductName, PackageFamilyName, FilePath
|
| Default value: | None |
| Required: | False |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
By default the module includes user PEs in the scan, but when you use this switch parameter, they won't be included. More info available on Microsoft Learn
| Type: | SwitchParameter |
|---|---|
| Position: | Named |
| Default value: | None |
| Required: | False |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
More info available on Microsoft Learn
| Type: | SwitchParameter |
|---|---|
| Position: | Named |
| Default value: | None |
| Required: | False |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |

New-DenyWDACConfig
[-Drivers]
-PolicyName <String>
[-ScanLocations <DirectoryInfo[]>]
[-Deploy]
[-Confirm]
[<CommonParameters>]Creates a Deny base policy by scanning a directory, this parameter uses DriverFile objects so it's best suitable for driver files. The base policy will have 2 allow all rules, meaning it can be deployed as a standalone base policy, side-by-side any other Base/Supplemental policies.
Note
The scan uses WHQLFilePublisher level without any fallbacks, and includes both usermode and kernel mode drivers.
Add a descriptive name for the Deny base policy. Accepts only alphanumeric and space characters.
| Type: | String |
|---|---|
| Position: | Named |
| Default value: | None |
| Required: | True |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Accepts one or more comma separated folder paths. Supports argument completion, when you press tab, folder picker GUI will open allowing you to easily select a folder, you can then add a comma , and press tab again to select another folder path or paste a folder path manually, works both ways.
| Type: | DirectoryInfo[] |
|---|---|
| Position: | Named |
| Default value: | None |
| Required: | True |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Indicates that the module will automatically deploy the Deny base policy after creation.
| Type: | SwitchParameter |
|---|---|
| Position: | Named |
| Default value: | None |
| Required: | False |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |

New-DenyWDACConfig
[-InstalledAppXPackages]
-PackageName <String>
-PolicyName <String>
[-Deploy]
[-Force]
[-Confirm]
[<CommonParameters>]Creates a Deny base policy for one or more installed Windows Apps (Appx) based on their PFN (Package Family Name). The base policy will have 2 allow all rules, meaning it can be deployed as a standalone base policy, side-by-side any other Base/Supplemental policies.
Enter the package name of an installed app. Supports wildcard * character. e.g, *Edge* or "*Microsoft*".
| Type: | String |
|---|---|
| Position: | Named |
| Default value: | None |
| Required: | True |
| Accept pipeline input: | False |
| Accept wildcard characters: | True |
Add a descriptive name for the Deny base policy. Accepts only alphanumeric and space characters.
| Type: | String |
|---|---|
| Position: | Named |
| Default value: | None |
| Required: | True |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Indicates that the module will automatically deploy the Deny base policy after creation.
| Type: | SwitchParameter |
|---|---|
| Position: | Named |
| Default value: | None |
| Required: | False |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Indicates that the cmdlet won't ask for confirmation and will proceed with creating the deny policy.
| Type: | SwitchParameter |
|---|---|
| Position: | Named |
| Default value: | None |
| Required: | False |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |

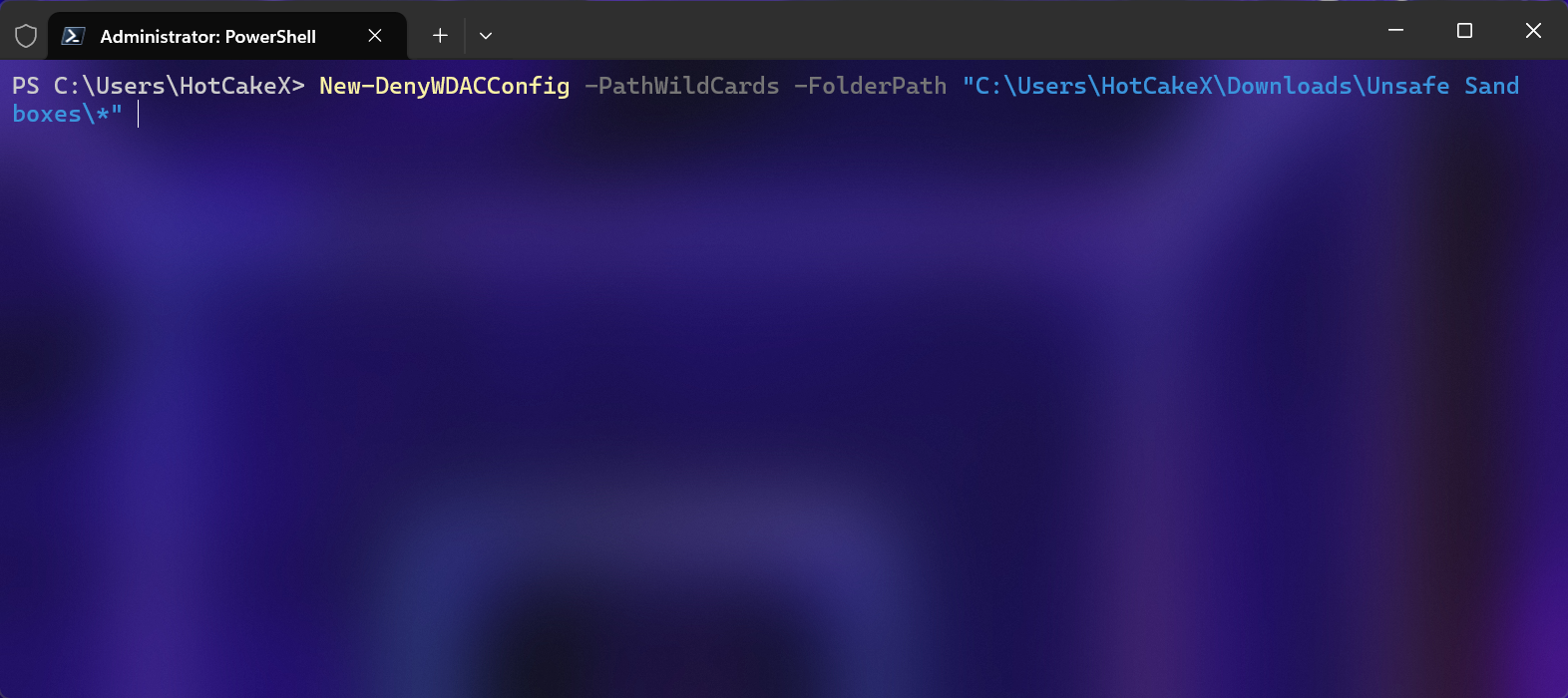
New-DenyWDACConfig
[-PathWildCards]
-PolicyName <String>
-FolderPath <DirectoryInfo>
[-Deploy]
[-Confirm]
[<CommonParameters>]Creates a Deny standalone base policy for a folder using wildcards. The base policy created by this parameter can be deployed side by side any other base/supplemental policy.
Note
This feature is also used internally by the Harden Windows Security Module.
Add a descriptive name for the Deny base policy. Accepts only alphanumeric and space characters.
| Type: | String |
|---|---|
| Position: | Named |
| Default value: | None |
| Required: | True |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
A folder path that includes at least one wildcard * character. Press TAB to open the folder picker GUI. Once you selected a folder, you will see the path will have \* at the end of it. You can modify the selected path by adding/removing wildcards * to it before proceeding.
| Type: | DirectoryInfo |
|---|---|
| Position: | Named |
| Default value: | None |
| Required: | True |
| Accept pipeline input: | False |
| Accept wildcard characters: | True |
Indicates that the module will automatically deploy the Deny base policy after creation.
| Type: | SwitchParameter |
|---|---|
| Position: | Named |
| Default value: | None |
| Required: | False |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
- Create AppControl Policy
- Create Supplemental Policy
- System Information
- Configure Policy Rule Options
- Simulation
- Allow New Apps
- Build New Certificate
- Create Policy From Event Logs
- Create Policy From MDE Advanced Hunting
- Create Deny Policy
- Merge App Control Policies
- Deploy App Control Policy
- Get Code Integrity Hashes
- Get Secure Policy Settings
- Update
- Sidebar
- Introduction
- App Control for Lightly Managed Devices
- App Control for Fully managed device - Variant 1
- App Control for Fully managed device - Variant 2
- App Control for Fully managed device - Variant 3
- App Control for Fully managed device - Variant 4
- App Control Notes
- How to Create and Deploy a Signed App Control Policy
- Fast and Automatic Microsoft Recommended Driver Block Rules updates
- App Control policy for BYOVD Kernel mode only protection
- EKUs in App Control for Business Policies
- App Control Rule Levels Comparison and Guide
- Script Enforcement and PowerShell Constrained Language Mode in App Control Policies
- How to Use Microsoft Defender for Endpoint Advanced Hunting With App Control
- App Control Frequently Asked Questions (FAQs)
- Create Bootable USB flash drive with no 3rd party tools
- Event Viewer
- Group Policy
- How to compact your OS and free up extra space
- Hyper V
- Overrides for Microsoft Security Baseline
- Git GitHub Desktop and Mandatory ASLR
- Signed and Verified commits with GitHub desktop
- About TLS, DNS, Encryption and OPSEC concepts
- Things to do when clean installing Windows
- Comparison of security benchmarks
- BitLocker, TPM and Pluton | What Are They and How Do They Work
- How to Detect Changes in User and Local Machine Certificate Stores in Real Time Using PowerShell
- Cloning Personal and Enterprise Repositories Using GitHub Desktop
- Only a Small Portion of The Windows OS Security Apparatus
- Rethinking Trust: Advanced Security Measures for High‐Stakes Systems
- Clean Source principle, Azure and Privileged Access Workstations
- How to Securely Connect to Azure VMs and Use RDP
- Basic PowerShell tricks and notes
- Basic PowerShell tricks and notes Part 2
- Basic PowerShell tricks and notes Part 3
- Basic PowerShell tricks and notes Part 4
- Basic PowerShell tricks and notes Part 5
- How To Access All Stream Outputs From Thread Jobs In PowerShell In Real Time
- PowerShell Best Practices To Follow When Coding
- How To Asynchronously Access All Stream Outputs From Background Jobs In PowerShell
- Powershell Dynamic Parameters and How to Add Them to the Get‐Help Syntax
- RunSpaces In PowerShell
- How To Use Reflection And Prevent Using Internal & Private C# Methods in PowerShell